Part 1 – What is the problem
Part 2 – ( This Post ) Installing a simple Linux Reverse Proxy on the same box ( 20 mins )
Part 3 – Converting your Domino SSL Certificate to work with Apache (30 mins )
The Fix
This fix is to add an Apache Server in front of Domino where Domino is running on a Linux box. All of the web serving functionality will be handled by Apache.
It should take about 20 minutes.
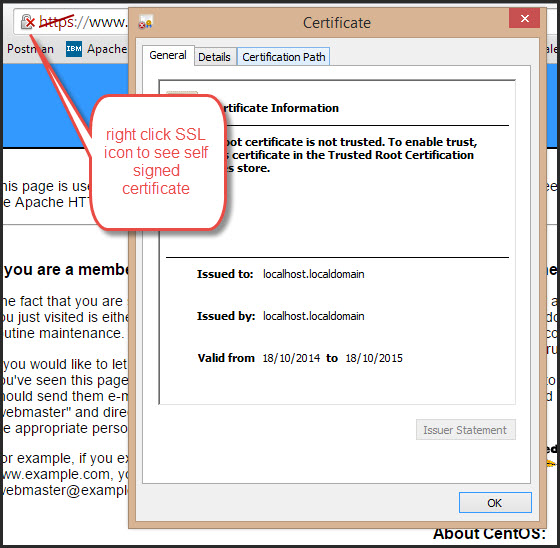
Note at the end of this step you will be using a self signed SSL certificate. Part 3 shows you how to convert your Domino SSL certificate for use with Apache but note that you will need a Windows XP machine ( no kidding ).
How it works
The domino web server will be changed to server only on port 8080 ( or similar ). Apache will listen for traffic on ports 80 and 443. When requests are received they are passed through to Domino in a transparent fashion.
The port 80 traffic is configured in /etc/httpf/conf/httpd.cong
The port 443 traffic is configured in /etc/httpd/conf.d/ssl.conf file
In the example below all traffic is redirected to SSL but you can change this if you want to use both port 80 and port 443
Step 1 – Change some Domino Settings
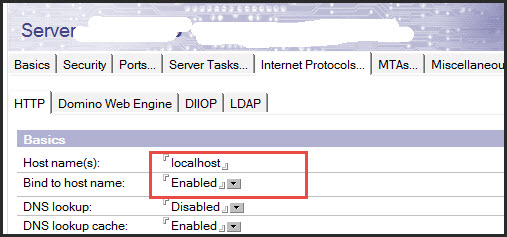
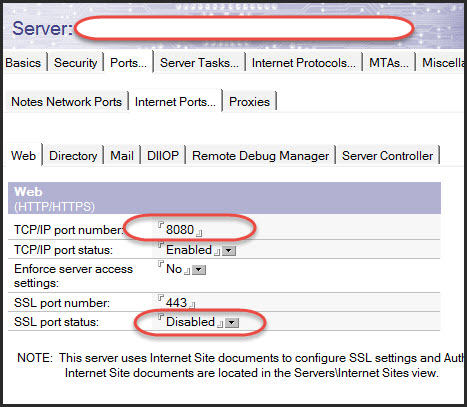
a) In the server document change the HTTP Port to 8080 or similar.
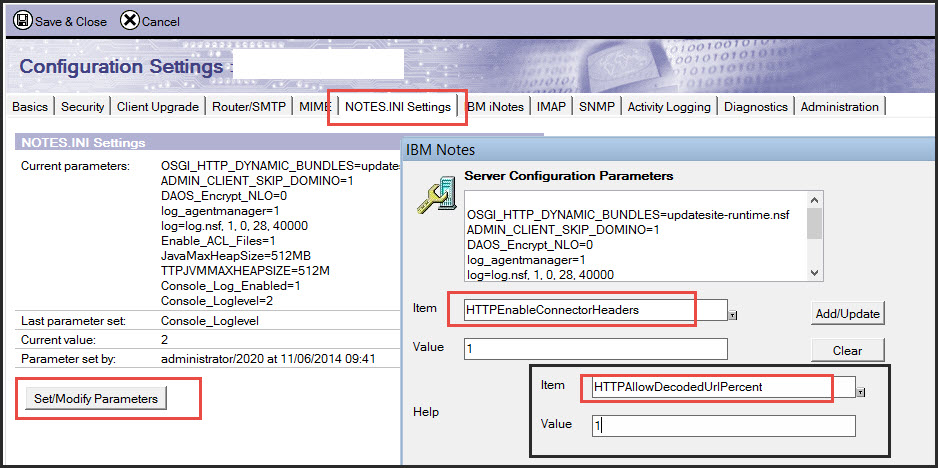
b) In the Notes.ini settings section of the configuration document make the following changes. Adding them here means that they are less likely to get forgotten at the next upgrade etc..
HTTPAllowDecodedUrlPercent = 1
HTTPEnableConnectorHeaders = 1 IMPORTANT – please see http://nevermind.dk/nevermind/blog.nsf/subject/security-hole-leaves-ibm-domino-server-wide-open—part-two
If you need to use the above notes ini variable then you must also add
RequestHeader unset “$WSRU”
to the httpd.conf and ssl.conf files in Apache
c) Check if any internet documents are set to force HTTP traffic to SSL and add a note to the Key file name field to remind you what you have done when you later have a senior moment.

d) restart the HTTP task
in the Domino console issue > tell http restart
this will free up port 80 for Apache to use.
e) Check that Domino is running on port 8080
note there may be firewall rules that need to be adjusted
http://yourserver.com:8080
Step 2 – Install Apache
Using the server console ( I use putty as it makes it easy to paste )
a) Update your Linux
>yum update
b) install Apache
>yum install httpd
c) install the SSL functionality
>yum install mod_ssl openssl
d) make Apache run on startup
>chkconfig –levels 235 httpd on
e) start Apache
>service httpd start
f) test Apache
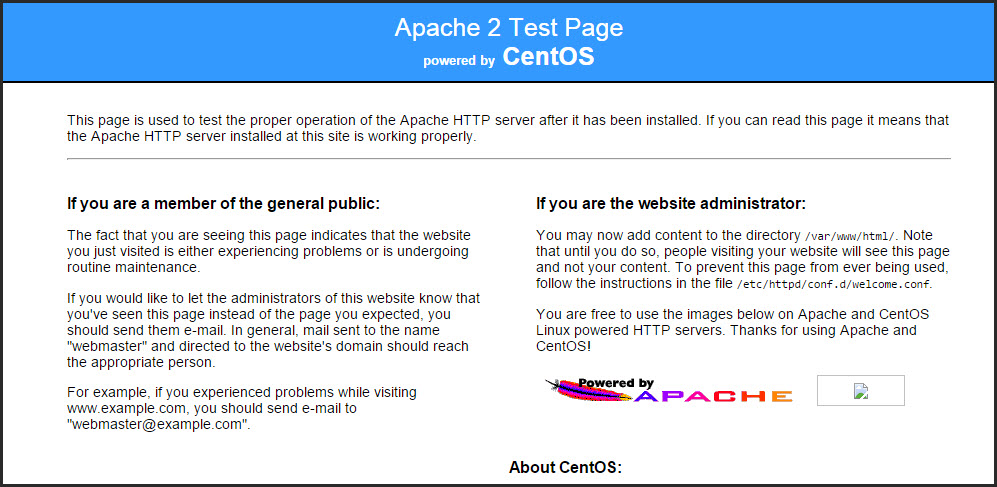
http://yourserver.com should show the Apache page below
https://yourserver.com should throw an SSL certificate error but then open
Step 3 – Configure Apache as a reverse proxy for Domino
Apache has a lot of functionality for Aliases so that you can manage multiple web domains on a single server. I have ignored this functionality for the most part to go for a very simple but effective scheme
The easiest way to copy and edit files on Linux is to use WinSCP
a) backup the default /etc/httpf/conf/httpd.cong file

b) in the /etc/httpf/conf/httpd.conf file add the following 12 lines
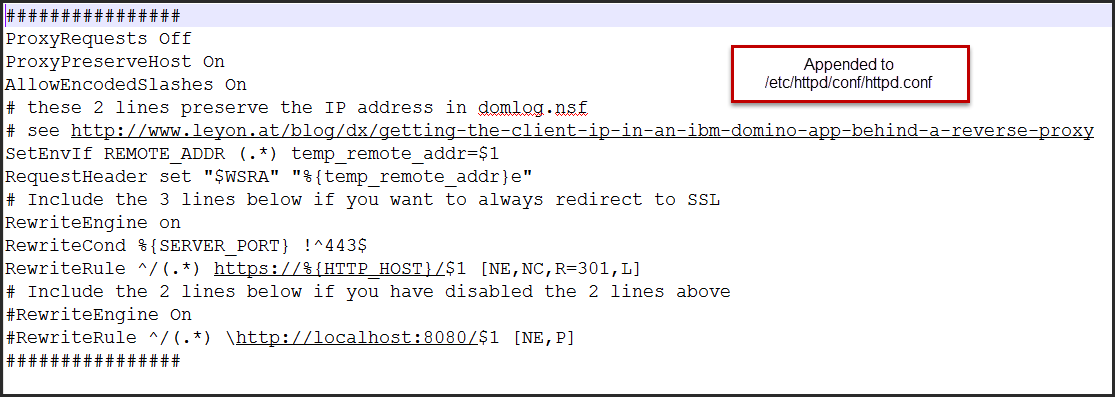
################
ProxyRequests Off
ProxyPreserveHost On
AllowEncodedSlashes On
# these 2 lines preserve the IP address in domlog.nsf
# see http://www.leyon.at/blog/dx/getting-the-client-ip-in-an-ibm-domino-app-behind-a-reverse-proxy
SetEnvIf REMOTE_ADDR (.*) temp_remote_addr=$1
RequestHeader set “$WSRA” “%{temp_remote_addr}e”
# Include the 3 lines below if you want to always redirect to SSL
RewriteEngine on
RewriteCond %{SERVER_PORT} !^443$
RewriteRule ^/(.*) https://%{HTTP_HOST}/$1 [NE,NC,R=301,L]
# Include the 2 lines below if you have disabled the 2 lines above
#RewriteEngine On
#RewriteRule ^/(.*) http://localhost:8080/$1 [NE,P]
################
The AllowEncoded slashes is needed for some XPages and QuickR functionality.
The RewriteCond %{SERVER_PORT} !^443$ and RewriteRule ^/(.*) https://%{HTTP_HOST}/$1 [NC,R=301,L] statement will redirect all non HTTPS traffic to HTTPS. If you do not want this to happen then comment out these lines and uncomment the next 2 lines.
The RewriteRule ^/(.*) http://localhost:8080/$1 [P] line will redirect all traffic to Domino on Port 8080. It is not required here if all traffic will be SSL as it is specified in the /etc/httpd/conf.d/ssl.conf file
Update : The NE attribute is explained in this post
c) backup the default /etc/httpd/conf.d/ssl.conf file
d) add the following 5 lines to the /etc/httpd/conf.d/ssl.conf file
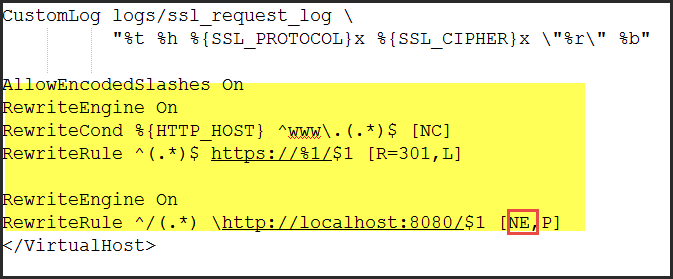
###################################
AllowEncodedSlashes On
RewriteEngine On
RewriteCond %{HTTP_HOST} ^www.(.*)$ [NC]
RewriteRule ^(.*)$ https://%1/$1 [R=301,L]
RewriteEngine On
RewriteRule ^/(.*) http://localhost:8080/$1 [NE,P]
######################################
I was surprised that the AllowEncodedSlashes On needed to be stated again but it does as I found out when our Font Awesome functionality stopped working in XPages.
e) in /etc/httpd/conf.d/ssl.conf file disable the use of SSL V3

f) restart Apache
>service httpd restart
g) test the server
http://myserver.com should redirect to https://myserver.com
the Domino content should be served up
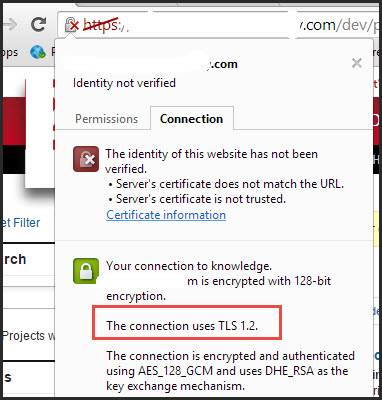
h) test that the connection is TLS1.2 rather than SSL V3
Step 4 – Block users from accessing Domino via port 8080
Conclusion
Your Domino http content is now being server via a modern web server that can use SHA-2 and TLS. It is still using the self signed SSL certificate but you can create a new one – all of the SSL providers have instructions for Apache or you can use Part 3 of the series to convert your existing SSL certificate to Apache.